Netbox DDOS Protector
NetBox DDoS Protector is a scalable solution that defends websites from DDoS attacks with real-time detection, BGP-based protection, and robust traffic filtering, ensuring uninterrupted service and reliability.
NetBox DDoS Protector is a cutting-edge, robust, and scalable solution designed to safeguard websites and digital infrastructures from Distributed Denial of Service (DDoS) attacks, ensuring uninterrupted service and seamless user experiences even under aggressive attack scenarios. Powered by advanced threat detection and mitigation technologies, NetBox offers real-time threat detection to instantly identify and neutralize malicious traffic, scalable protection adaptable to businesses of all sizes, and comprehensive reporting with actionable analytics. Operating in cluster mode for high availability and seamless scaling, NetBox features advanced rate limiting for fair resource allocation, powerful network filtering to prevent unauthorized access, and BGP-based protection for an extra layer of defense against large-scale DDoS attacks. Easily integrating into existing network infrastructures for quick deployment, NetBox empowers businesses to protect critical assets 24/7, maintain business continuity, and operate with confidence against evolving cyber threats.
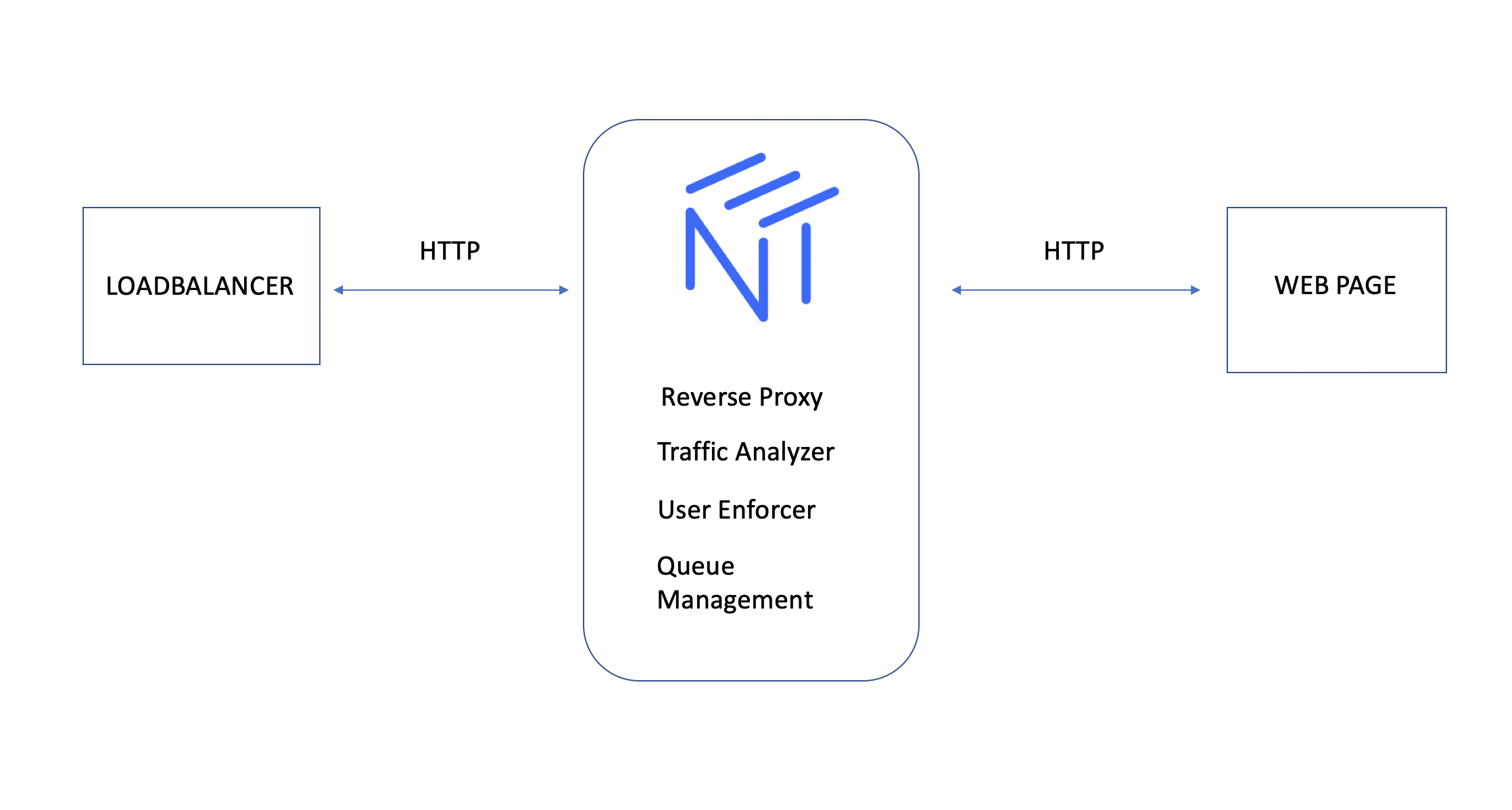
NetBox DDoS Protector operates through a multi-layered approach to detect, mitigate, and prevent Distributed Denial of Service (DDoS) attacks in real time. It begins by monitoring incoming traffic patterns using advanced algorithms and AI-driven threat intelligence to identify anomalies indicative of malicious activity. Once detected, the system applies rate limiting and traffic filtering rules to ensure fair resource allocation and block unauthorized or harmful requests. NetBox leverages cluster mode for high availability, distributing the load across multiple nodes to prevent single points of failure. Its support for BGP-based protection enables it to reroute traffic through scrubbing centers, effectively neutralizing large-scale attacks before they reach the target infrastructure. By analyzing traffic in real time and employing adaptive countermeasures, NetBox ensures your website and applications remain secure, operational, and resilient against evolving cyber threats.
Article last updated: 2026-01-29T14:19:22.454Z